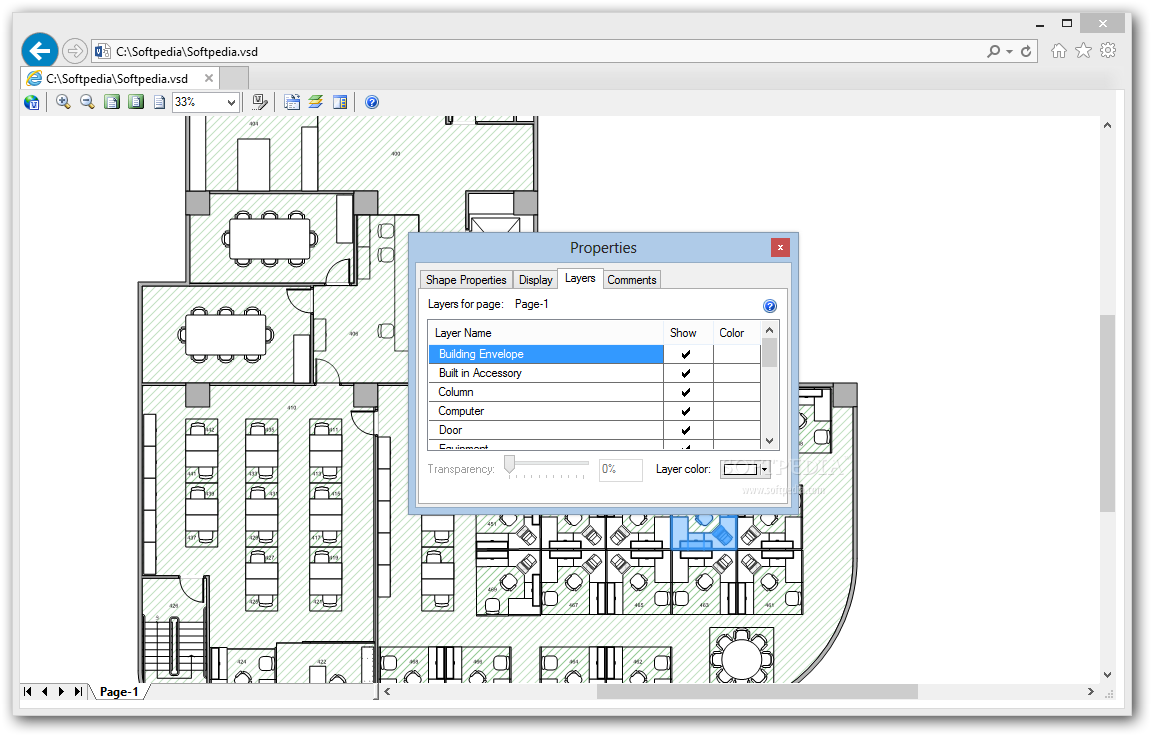
Microsoft Visio 2013 Viewer allows anyone to view Visio drawings inside their Microsoft Internet Explorer Web browser. Visio users can freely distribute Visio drawings. ★ Supported file types:.vsd,.vdx and.vsdx ★ Supported versions: 2007, 2010, 2013, 2016 Once you’ve installed the extension, you can: ★ Open Visio files from your computer: Click the Lucidchart icon on your toolbar and select “Choose file”, or drag and drop your Visio file onto the page. Visio Viewer not working I installed visio viewr 2007 (and the update for it) but it is not working as exepcted. When I click on a visio file in an email or on the hard disk internet explorer 7 opens in the restricted sites zone and all I see is blank page. To view this vulnerability as a standard entry in the Common Vulnerabilities and Exposures list, see CVE-2013-1301. Mitigating Factors Mitigation refers to a setting, common configuration, or general best-practice, existing in a default state, that could reduce the severity of exploitation of a vulnerability.
- Vsdx Viewer
- Microsoft Visio Viewer 2013
- Visio Viewer 2013 Location
- What Is Microsoft Office Visio Viewer 2013
Findings (MAC III - Administrative Sensitive)
| Finding ID | Severity | Title | Description |
|---|---|---|---|
| V-40741 | Medium | ActiveX installs must be configured for proper restrictions. | Microsoft ActiveX controls allow unmanaged, unprotected code to run on the user computers. ActiveX controls do not run within a protected container in the browser like the other types of HTML or .. |
| V-40740 | Medium | Protection from zone elevation must be enforced. | Internet Explorer places restrictions on each web page users can use the browser to open. Web pages on a user's local computer have the fewest security restrictions and reside in the Local Machine .. |
| V-40742 | Medium | Warning Bar settings for VBA macros must be configured. | When users open files containing VBA Macros, applications open the files with the macros disabled and displays the Trust Bar with a warning that macros are present and have been disabled. Users .. |
| V-40734 | Medium | Scripted Window Security must be enforced. | Malicious websites often try to confuse or trick users into giving a site permission to perform an action allowing the site to take control of the users' computers in some manner. Disabling or not .. |
| V-40735 | Medium | Add-on Management functionality must be allowed. | Internet Explorer add-ons are pieces of code, run in Internet Explorer, to provide additional functionality. Rogue add-ons may contain viruses or other malicious code. Disabling or not configuring .. |
| V-40736 | Medium | Add-ins to Office applications must be signed by a Trusted Publisher. | Office 2013 applications do not check the digital signature on application add-ins before opening them. Disabling or not configuring this setting may allow an application to load a dangerous .. |
| V-40737 | Medium | Links that invoke instances of IE from within an Office product must be blocked. | The Pop-up Blocker feature in Internet Explorer can be used to block most unwanted pop-up and pop-under windows from appearing. This functionality can be controlled separately for instances of .. |
| V-40730 | Medium | Disabling of user name and password syntax from being used in URLs must be enforced. | The Uniform Resource Locator (URL) standard allows user authentication to be included in URL strings in the form http://username:password@example.com. A malicious user might use this URL syntax to .. |
| V-40731 | Medium | The Internet Explorer Bind to Object functionality must be enabled. | Internet Explorer performs a number of safety checks before initializing an ActiveX control. It will not initialize a control if the kill bit for the control is set in the registry, or if the .. |
| V-40732 | Medium | The Saved from URL mark must be selected to enforce Internet zone processing. | Typically, when Internet Explorer loads a web page from a Universal Naming Convention (UNC) share that contains a Mark of the Web (MOTW) comment, indicating the page was saved from a site on the .. |
| V-40733 | Medium | Navigation to URLs embedded in Office products must be blocked. | To protect users from attacks, Internet Explorer usually does not attempt to load malformed URLs. This functionality can be controlled separately for instances of Internet Explorer spawned by .. |
| V-40738 | Medium | Trust Bar Notifications for unsigned applications must be disabled. | If an application is configured to require all add-ins to be signed by a trusted publisher, any unsigned add-ins the application loads will be disabled and the application will display the Trust .. |
| V-40739 | Medium | File downloads must be configured for proper restrictions. | Disabling this setting allows websites to present file download prompts via code without the user specifically initiating the download. User preferences may also allow the download to occur .. |
Security Bulletin
Vulnerability in Microsoft Visio Viewer 2010 Could Allow Remote Code Execution (2801261)
Published: March 12, 2013 | Updated: September 25, 2013
Version: 1.3
General Information
Executive Summary
This security update resolves a privately reported vulnerability in Microsoft Office. Workforce compound miter saw. The vulnerability could allow remote code execution if a user opens a specially crafted Visio file. An attacker who successfully exploited the vulnerability could gain the same user rights as the current user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
This security update is rated Critical for all supported editions of Microsoft Visio Viewer 2010. For more information, see the subsection, Affected and Non-Affected Software, in this section.
The security update addresses the vulnerability by modifying the way that Microsoft Visio Viewer allocates memory when parsing specially crafted Visio files. Download company of heroes 2 full crack. For more information about the vulnerabilities, see the Frequently Asked Questions (FAQ) subsection for the specific vulnerability entry under the next section, Vulnerability Information.
Recommendation. Customers can configure automatic updating to check online for updates from Microsoft Update by using the Microsoft Update service. Customers who have automatic updating enabled and configured to check online for updates from Microsoft Update typically will not need to take any action because this security update will be downloaded and installed automatically. Customers who have not enabled automatic updating need to check for updates from Microsoft Update and install this update manually. For information about specific configuration options in automatic updating in supported editions of Windows XP and Windows Server 2003, see Microsoft Knowledge Base Article 294871. For information about automatic updating in supported editions of Windows Vista, Windows Server 2008, Windows 7, and Windows Server 2008 R2, see Understanding Windows automatic updating.
For administrators and enterprise installations, or end users who want to install this security update manually, Microsoft recommends that customers apply the update immediately using update management software, or by checking for updates using the Microsoft Update service.
See also the section, Detection and Deployment Tools and Guidance, later in this bulletin.
Knowledge Base Article
Vsdx Viewer
| Knowledge Base Article | 2801261 |
|---|---|
| File information | Yes |
| SHA1/SHA2 hashes | Yes |
| Known issues | None |
Affected and Non-Affected Software
The following software have been tested to determine which versions or editions are affected. Other versions or editions are either past their support life cycle or are not affected. To determine the support life cycle for your software version or edition, visit Microsoft Support Lifecycle.
Affected Software
| Office Software | Maximum Security Impact | Aggregate Severity Rating | Updates Replaced |
|---|---|---|---|
| Microsoft Visio Viewer 2010 Service Pack 1 (32-bit Edition) (2687505) | Remote Code Execution | Critical | 2598287 in MS12-059 |
| Microsoft Visio Viewer 2010 Service Pack 1 (64-bit Edition) (2687505) | Remote Code Execution | Critical | 2598287 in MS12-059 |
| Microsoft Visio 2010 Service Pack 1 (32-bit editions) (2760762) | None | No severity rating[1] | 2687508 in MS12-059 |
| Microsoft Visio 2010 Service Pack 1 (64-bit editions) (2760762) | None | No severity rating[1] | 2687508 in MS12-059 |
| Microsoft Office 2010 Filter Pack Service Pack 1 (32-bit version) (2553501) | Remote Code Execution | Critical | None |
| Microsoft Office 2010 Filter Pack Service Pack 1 (64-bit version) (2553501) | Remote Code Execution | Critical | None |
Microsoft Visio Viewer 2013
| Affected Software | Visio Viewer Tree Object Type Confusion Vulnerability - CVE-2013-0079 | Aggregate Severity Rating |
|---|---|---|
| Microsoft Visio Viewer 2010 Service Pack 1 (32-bit Edition) | Critical Remote Code Execution | Critical |
| Microsoft Visio Viewer 2010 Service Pack 1 (64-bit Edition) | Critical Remote Code Execution | Critical |
| Microsoft Visio 2010 Service Pack 1 (32-bit editions) | No severity rating[1] | No severity rating |
| Microsoft Visio 2010 Service Pack 1 (64-bit editions) | No severity rating[1] | No severity rating |
| Microsoft Office 2010 Filter Pack Service Pack 1 (32-bit version) | Critical Remote Code Execution | Critical |
| Microsoft Office 2010 Filter Pack Service Pack 1 (64-bit version) | Critical Remote Code Execution | Critical |
Visio Viewer 2013 Location
[1]Severity ratings do not apply to this update for the specified software because the known attack vectors for the vulnerability are blocked. Visio Viewer Tree Object Type Confusion Vulnerability - CVE-2013-0079 --------------------------------------------------------------------- A remote code execution vulnerability exists in the way that Microsoft Visio Viewer handles memory when rendering specially crafted Visio files. An attacker who successfully exploited this vulnerability could take complete control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less affected than users who operate with administrative user rights. To view this vulnerability as a standard entry in the Common Vulnerabilities and Exposures list, see [CVE-2013-0079](http://www.cve.mitre.org/cgi-bin/cvename.cgi?name=cve-2013-0079). #### Mitigating Factors Mitigation refers to a setting, common configuration, or general best-practice, existing in a default state, that could reduce the severity of exploitation of a vulnerability. The following mitigating factors may be helpful in your situation: - By default, all supported versions of Microsoft Outlook, Microsoft Outlook Express, and Windows Mail open HTML email messages in the Restricted sites zone. The Restricted sites zone, which disables script and ActiveX controls, helps reduce the risk of an attacker being able to use this vulnerability to execute malicious code. If a user clicks a link in an email message, the user could still be vulnerable to exploitation of this vulnerability through the web-based attack scenario. - By default, Internet Explorer on Windows Server 2003, Windows Server 2008, Windows Server 2008 R2, and Windows Server 2012 runs in a restricted mode that is known as [Enhanced Security Configuration](http://technet.microsoft.com/library/dd883248). This mode mitigates this vulnerability. See the FAQ section for this vulnerability for more information about Internet Explorer Enhanced Security Configuration. - In a web-based attack scenario, an attacker could host a website that contains a specially crafted Visio file that is used to attempt to exploit this vulnerability. In addition, compromised websites and websites that accept or host user-provided content or advertisements could contain specially crafted content that could exploit this vulnerability. In all cases, however, an attacker would have no way to force users to visit these websites. Instead, an attacker would have to convince users to visit the website, typically by getting them to click a link in an email message or Instant Messenger message that takes users to the attacker’s website, and convince them to open the specially crafted Visio file. - An attacker who successfully exploited this vulnerability could gain the same user rights as the current user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. #### Workarounds Workaround refers to a setting or configuration change that does not correct the underlying vulnerability but would help block known attack vectors before you apply the update. Microsoft has tested the following workarounds and states in the discussion whether a workaround reduces functionality: - **Set Internet and Local intranet security zone settings to 'High' to block ActiveX Controls and Active Scripting in these zones** You can help protect against exploitation of this vulnerability by changing your settings for the Internet security zone to block ActiveX controls and Active Scripting. You can do this by setting your browser security to High. To raise the browsing security level in Internet Explorer, perform the following steps: 1. On the Internet Explorer **Tools** menu, click **Internet Options**. 2. In the **Internet Options** dialog box, click the **Security** tab, and then click **Internet**. 3. Under **Security level for this zone**, move the slider to **High**. This sets the security level for all websites you visit to High. 4. Click **Local intranet**. 5. Under **Security level for this zone**, move the slider to **High**. This sets the security level for all websites you visit to High. 6. Click **OK** to accept the changes and return to Internet Explorer. **Note** If no slider is visible, click **Default Level**, and then move the slider to **High**. **Note** Setting the level to High may cause some websites to work incorrectly. If you have difficulty using a website after you change this setting, and you are sure the site is safe to use, you can add that site to your list of trusted sites. This will allow the site to work correctly even with the security setting set to High. **Impact of workaround.** There are side effects to blocking ActiveX Controls and Active Scripting. Many websites that are on the Internet or on an intranet use ActiveX or Active Scripting to provide additional functionality. For example, an online e-commerce site or banking site may use ActiveX Controls to provide menus, ordering forms, or even account statements. Blocking ActiveX Controls or Active Scripting is a global setting that affects all Internet and intranet sites. If you do not want to block ActiveX Controls or Active Scripting for such sites, use the steps outlined in 'Add sites that you trust to the Internet Explorer Trusted sites zone'. **Add sites that you trust to the Internet Explorer Trusted sites zone** After you set Internet Explorer to block ActiveX controls and Active Scripting in the Internet zone and in the Local intranet zone, you can add sites that you trust to the Internet Explorer Trusted sites zone. This will allow you to continue to use trusted websites exactly as you do today, while helping to protect yourself from this attack on untrusted sites. We recommend that you add only sites that you trust to the Trusted sites zone. To do this, perform the following steps: 1. In Internet Explorer, click **Tools**, click **Internet Options**, and then click the **Security** tab. 2. In the **Select a web content zone to specify its current security settings** box, click **Trusted Sites**, and then click **Sites**. 3. If you want to add sites that do not require an encrypted channel, click to clear the **Require server verification (https:) for all sites in this zone** check box. 4. In the **Add this website to the zone** box, type the URL of a site that you trust, and then click **Add**. 5. Repeat these steps for each site that you want to add to the zone. 6. Click **OK** two times to accept the changes and return to Internet Explorer. **Note** Add any sites that you trust not to take malicious action on your system. Two in particular that you may want to add are ***.windowsupdate.microsoft.com** and ***.update.microsoft.com**. These are the sites that will host the update, and it requires an ActiveX Control to install the update. - **Configure Internet Explorer to prompt before running Active Scripting or to disable Active Scripting in the Internet and Local intranet security zone** You can help protect against exploitation of this vulnerability by changing your settings to prompt before running Active Scripting or to disable Active Scripting in the Internet and Local intranet security zone. To do this, perform the following steps: 1. In Internet Explorer, click **Internet Options** on the **Tools** menu. 2. Click the **Security** tab. 3. Click **Internet**, and then click **Custom Level**. 4. Under **Settings**, in the **Scripting** section, under **Active Scripting**, click **Prompt** or **Disable**, and then click **OK**. 5. Click **Local intranet**, and then click **Custom Level**. 6. Under **Settings**, in the **Scripting** section, under **Active Scripting**, click **Prompt** or **Disable**, and then click **OK**. 7. Click **OK** two times to return to Internet Explorer. **Note** Disabling Active Scripting in the Internet and Local intranet security zones may cause some websites to work incorrectly. If you have difficulty using a website after you change this setting, and you are sure the site is safe to use, you can add that site to your list of trusted sites. This will allow the site to work correctly. **Impact of workaround.** There are side effects to prompting before running Active Scripting. Many websites that are on the Internet or on an intranet use Active Scripting to provide additional functionality. For example, an online e-commerce site or banking site may use Active Scripting to provide menus, ordering forms, or even account statements. Prompting before running Active Scripting is a global setting that affects all Internet and intranet sites. You will be prompted frequently when you enable this workaround. For each prompt, if you feel you trust the site that you are visiting, click **Yes** to run Active Scripting. If you do not want to be prompted for all these sites, use the steps outlined in 'Add sites that you trust to the Internet Explorer Trusted sites zone'. **Add sites that you trust to the Internet Explorer Trusted sites zone** After you set Internet Explorer to require a prompt before it runs ActiveX controls and Active Scripting in the Internet zone and in the Local intranet zone, you can add sites that you trust to the Internet Explorer Trusted sites zone. This will allow you to continue to use trusted websites exactly as you do today, while helping to protect you from this attack on untrusted sites. We recommend that you add only sites that you trust to the Trusted sites zone. To do this, perform the following steps: 1. In Internet Explorer, click **Tools**, click **Internet Options**, and then click the **Security** tab. 2. In the **Select a web content zone to specify its current security settings** box, click **Trusted Sites**, and then click **Sites**. 3. If you want to add sites that do not require an encrypted channel, click to clear the **Require server verification (https:) for all sites in this zone** check box. 4. In the **Add this website to the zone** box, type the URL of a site that you trust, and then click **Add**. 5. Repeat these steps for each site that you want to add to the zone. 6. Click **OK** two times to accept the changes and return to Internet Explorer. **Note** Add any sites that you trust not to take malicious action on your system. Two in particular that you may want to add are ***.windowsupdate.microsoft.com** and ***.update.microsoft.com**. These are the sites that will host the update, and it requires an ActiveX Control to install the update. - **Do not open Office files that you receive from untrusted sources or that you receive unexpectedly from trusted sources** Do not open Office files that you receive from untrusted sources or that you receive unexpectedly from trusted sources. This vulnerability could be exploited when a user opens a specially crafted file. #### FAQ **What is the scope of the vulnerability?** This is a remote code execution vulnerability. **What causes the vulnerability?** The vulnerability is caused when Microsoft Visio does not properly handle memory when parsing specially crafted Visio files. **What might an attacker use the vulnerability to do?** An attacker who successfully exploited this vulnerability could run arbitrary code in the context of the current user. If the current user is logged on with administrative user rights, an attacker could take complete control of the affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. **How could an attacker exploit the vulnerability?** This vulnerability requires that a user open a specially crafted Visio file with an affected version of Microsoft Visio Viewer or index a specially crafted Visio file using Windows Search. In an email attack scenario, an attacker could exploit the vulnerability by sending a specially crafted Visio file to the user and by convincing the user to open the file. In a web-based attack scenario, an attacker would have to host a website that contains a specially crafted Visio file that is used to attempt to exploit this vulnerability. In addition, compromised websites and websites that accept or host user-provided content could contain specially crafted content that could exploit this vulnerability. An attacker would have no way to force users to visit a specially crafted website. Instead, an attacker would have to convince users to visit the website, typically by getting them to click a link that takes them to the attacker's site, which would automatically load the specially crafted Visio document in the browser. In a shared drive or folder attack scenario, an attacker could place a specially crafted Visio file on a shared drive or folder that then could be indexed by Windows Search running on a victim's system. **What systems are primarily at risk from the vulnerability?** Systems where Microsoft Visio Viewer is used, including workstations and terminal servers, are primarily at risk. Servers could be at more risk if administrators allow users to log on to servers and to run programs. However, best practices strongly discourage allowing this. **I am running Internet Explorer for Windows Server 2003, Windows Server 2008, Windows Server 2008 R2, or Windows Server 2012. Does this mitigate these vulnerabilities?** Yes. By default, Internet Explorer on Windows Server 2003, Windows Server 2008, Windows Server 2008 R2, and Windows Server 2012 runs in a restricted mode that is known as [Enhanced Security Configuration](http://technet.microsoft.com/library/dd883248). Enhanced Security Configuration is a group of preconfigured settings in Internet Explorer that can reduce the likelihood of a user or administrator downloading and running specially crafted web content on a server. This is a mitigating factor for websites that you have not added to the Internet Explorer Trusted sites zone. **What does the update do?** This update addresses the vulnerability by modifying the way that Microsoft Visio Viewer allocates memory when parsing specially crafted Visio files. **When this security bulletin was issued, had this vulnerability been publicly disclosed?** No. Microsoft received information about this vulnerability through coordinated vulnerability disclosure. **When this security bulletin was issued, had Microsoft received any reports that this vulnerability was being** **exploited?** No. Microsoft had not received any information to indicate that this vulnerability had been publicly used to attack customers when this security bulletin was originally issued. ### Update Information Detection and Deployment Tools and Guidance ------------------------------------------- Several resources are available to help administrators deploy security updates. - Microsoft Baseline Security Analyzer (MBSA) lets administrators scan local and remote systems for missing security updates and common security misconfigurations. - Windows Server Update Services (WSUS), Systems Management Server (SMS), and System Center Configuration Manager (SCCM) help administrators distribute security updates. - The Update Compatibility Evaluator components included with Application Compatibility Toolkit aid in streamlining the testing and validation of Windows updates against installed applications. For information about these and other tools that are available, see [Security Tools for IT Pros](http://technet.microsoft.com/security/cc297183). Security Update Deployment -------------------------- **Affected Software** For information about the specific security update for your affected software, click the appropriate link: #### Microsoft Visio Viewer 2010, Microsoft Visio 2010, and Microsoft Office 2010 Filter Packs (all editions) **Reference Table** The following table contains the security update information for this software.| Security update file names | For Microsoft Visio Viewer 2010 (32-bit Edition): vviewer2010-kb2687505-fullfile-x86-glb.exe |
| For Microsoft Visio Viewer 2010 (64-bit Edition): vviewer2010-kb2687505-fullfile-x64-glb.exe | |
| For Microsoft Visio 2010 (32-bit editions): visio2010-kb2760762-fullfile-x86-glb.exe | |
| For Microsoft Visio 2010 (64-bit editions): visio2010-kb2760762-fullfile-x64-glb.exe | |
| For Microsoft Office 2010 Filter Packs (32-bit version): filterpack2010-kb2553501-fullfile-x86-glb.exe | |
| For Microsoft Office 2010 Filter Packs (64-bit version): filterpack2010-kb2553501-fullfile-x64-glb.exe | |
| Installation switches | See Microsoft Knowledge Base Article 912203 |
| Restart requirement | In some cases, this update does not require a restart. If the required files are being used, this update will require a restart. If this behavior occurs, a message appears that advises you to restart. To help reduce the chance that a restart will be required, stop all affected services and close all applications that may use the affected files prior to installing the security update. For more information about the reasons why you may be prompted to restart, see Microsoft Knowledge Base Article 887012. |
| Removalinformation | Use Add or Remove Programs item in Control Panel. |
| File information | For Microsoft Visio Viewer 2010: see Microsoft Knowledge Base Article 2687505 |
| For Microsoft Visio 2010: see Microsoft Knowledge Base Article 2760762 | |
| For Microsoft Office 2010 Filter Packs: see Microsoft Knowledge Base Article 2553501 | |
| Registry key verification | Not applicable |
What Is Microsoft Office Visio Viewer 2013
### Other Information #### Acknowledgments Microsoft [thanks](http://go.microsoft.com/fwlink/?linkid=21127) the following for working with us to help protect customers: - [Aniway.Anyway@gmail.com](mailto:aniway.anyway@gmail.com), working with [VeriSign iDefense Labs](http://labs.idefense.com/), for reporting the Visio Viewer Tree Object Type Confusion Vulnerability (CVE-2013-0079) - Will Dormann of the [CERT/CC](http://www.cert.org/) for reporting the Visio Viewer Tree Object Type Confusion Vulnerability (CVE-2013-0079) #### Microsoft Active Protections Program (MAPP) To improve security protections for customers, Microsoft provides vulnerability information to major security software providers in advance of each monthly security update release. Security software providers can then use this vulnerability information to provide updated protections to customers via their security software or devices, such as antivirus, network-based intrusion detection systems, or host-based intrusion prevention systems. To determine whether active protections are available from security software providers, please go to the active protections websites provided by program partners, listed in [Microsoft Active Protections Program (MAPP) Partners](http://go.microsoft.com/fwlink/?linkid=215201). #### Support **How to obtain help and support for this security update** - Help installing updates: [Support for Microsoft Update](http://support.microsoft.com/ph/6527) - Security solutions for IT professionals: [TechNet Security Troubleshooting and Support](http://technet.microsoft.com/security/bb980617.aspx) - Help protect your computer that is running Windows from viruses and malware: [Virus Solution and Security Center](http://support.microsoft.com/contactus/cu_sc_virsec_master) - Local support according to your country: [International Support](http://support.microsoft.com/common/international.aspx) #### Disclaimer The information provided in the Microsoft Knowledge Base is provided 'as is' without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply. #### Revisions - V1.0 (March 12, 2013): Bulletin published. - V1.1 (March 15, 2013): Clarified language in the vulnerability FAQ, **How could an attacker exploit the vulnerability?** - V1.2 (September 18, 2013): Corrected language in the vulnerability FAQ, **How could an attacker exploit the vulnerability?** This is an informational change only. - V1.3 (September 25, 2013): Corrected the severity rating and impact for the Microsoft Office 2010 Filter Pack update (2553501). Customers who have already successfully applied this update do not need to take any action. Customers running the affected software who have not applied this update may need to re-evaluate whether or not to apply the update based on these changes. See Update FAQ for details. *Built at 2014-04-18T13:49:36Z-07:00*